
Hardware Security Modules
Why
A hardware security module (HSM) is a dedicated, tamper-resistant physical device that generates, stores, and manages cryptographic keys within a hardened security boundary. Unlike software-based key storage, an HSM ensures that private keys never leave the protected hardware environment, providing the highest level of assurance for organisations that depend on digital trust.
Unsung delivers end-to-end HSM services — from architecture design and vendor selection through to deployment, migration, and ongoing operational support. Our vendor-certified consultants work with Thales, Crypto4A, Fortanix, and Futurex platforms, serving government, defence, and enterprise clients across the United Kingdom.
What Is a Hardware Security Module?
A hardware security module is a purpose-built cryptographic appliance designed to perform key generation, digital signing, encryption, and decryption operations within a physically protected enclosure. HSMs are engineered to be tamper-resistant and tamper-evident: if someone attempts to physically access the internal components, the device detects the intrusion and automatically destroys (zeroises) the keys it holds.
HSMs are validated against internationally recognised standards, most notably FIPS 140-2 Level 3 and its successor FIPS 140-3 Level 3, as well as Common Criteria. FIPS 140-2 Level 3 validation requires physical tamper-resistance mechanisms, identity-based authentication for all operators, and logical separation between the interfaces through which critical security parameters enter and leave the module.
The fundamental difference between an HSM and software-based key storage is the security boundary. When cryptographic keys are stored in software — on a server’s file system, within a database, or in a virtual machine — they are exposed to the same attack surface as the operating system and applications around them. A compromised server means compromised keys. An HSM creates an isolated environment where keys are generated and used but never exported in plaintext, dramatically reducing the risk of key compromise.
Modern HSMs support a wide range of cryptographic algorithms including RSA, ECC (elliptic curve cryptography), AES, and increasingly post-quantum algorithms such as ML-DSA and ML-KEM. They serve as the trust anchor for public key infrastructure (PKI), certificate lifecycle management, code signing, payment processing, and digital identity systems.
What
HSM Architecture and Deployment Models
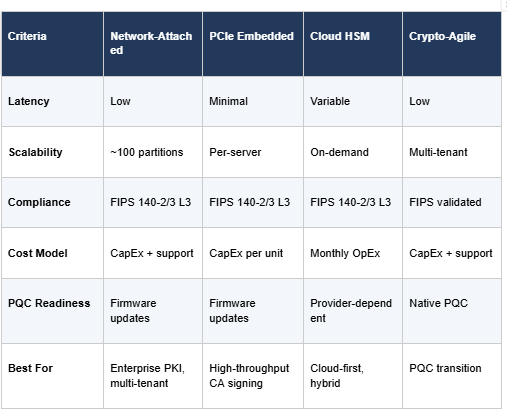
Choosing the right HSM deployment model depends on your organisation’s performance requirements, regulatory obligations, infrastructure strategy, and long-term cryptographic roadmap. There are four primary deployment models available today, each with distinct advantages.
Network-Attached HSMs
Network-attached HSMs, such as the Thales Luna Network HSM 7, are standalone appliances connected to your data centre network. They support approximately 100 isolated partitions, enabling multi-tenant separation where different applications, teams, or clients share a single physical device without accessing each other’s keys. Network HSMs are the most common deployment model for enterprise PKI, offering high availability configurations and centralised management.
PCIe Embedded HSMs
PCIe HSMs, such as the Thales Luna PCIe HSM 7, are installed directly into a server’s expansion slot. By eliminating the network hop between the application and the cryptographic module, PCIe HSMs deliver minimal latency and maximum throughput. They are particularly well-suited for high-volume transaction processing, certificate authority (CA) signing operations, and performance-critical workloads where every millisecond matters.
Cloud HSMs
Cloud HSM services, including Thales Luna Cloud HSM and Futurex VirtuCrypt, deliver hardware-grade key protection without on-premises infrastructure. Keys remain in dedicated hardware but the service is consumed on a subscription basis. Cloud HSMs are ideal for organisations pursuing cloud-first strategies, hybrid environments, or those that need to scale cryptographic capacity without capital expenditure on physical appliances.
Crypto-Agile HSMs
Crypto-agile HSMs, such as the Crypto4A QxHSM, are purpose-built to support both classical and post-quantum cryptographic algorithms natively. As organisations prepare for the transition to post-quantum cryptography (PQC), crypto-agile HSMs provide a future-proof foundation that avoids costly hardware replacement when new algorithm standards are mandated.
Deployment Model Comparison
HSM Use Cases
Hardware security modules underpin the most critical trust operations across government, financial services, defence, and enterprise environments. Below are the primary use cases where HSM protection is either mandated by regulation or considered essential best practice.
PKI Root and Issuing CA Key Protection
The private keys of root and issuing certificate authorities are the foundation of your entire PKI trust chain. If a CA key is compromised, every certificate it has issued becomes untrustworthy. HSMs protect these keys within FIPS 140-2 Level 3 validated hardware, ensuring they are generated, stored, and used exclusively within the secure boundary. Unsung has delivered highly assured PKI root deployments for government and enterprise clients, with HSM-backed key protection as a core component of every PKI Design & Build engagement.
Code Signing Key Management
Software supply chain security depends on the integrity of code signing keys. Storing signing keys on developer workstations or shared network drives creates unacceptable risk — a stolen signing key allows an attacker to distribute malicious software that appears legitimate. HSMs centralise signing key storage with strict access controls, workflow approvals, and comprehensive audit trails. Unsung implements HSM-backed code signing solutions using Keyfactor Enterprise Code Signing and Keyfactor Signum for on-premises and cloud-hosted environments respectively.
Payment Transaction Processing
The Payment Card Industry Data Security Standard (PCI DSS) requires that cryptographic keys used in payment processing are protected within validated hardware. HSMs perform PIN translation, card verification, and transaction authorisation within a certified security boundary, meeting the requirements of PCI HSM and PCI DSS compliance. Organisations in financial services rely on HSMs to protect cardholder data and maintain payment scheme certification.
Digital Signature Generation
Qualified electronic signatures under eIDAS and other regulatory frameworks require that signing keys are held within a qualified signature creation device. HSMs fulfil this requirement, generating signatures within a tamper-resistant boundary and ensuring the signatory retains sole control of their key. Remote signing platforms integrate with HSMs to enable server-side signing with strong authentication.
Key Management for Encryption at Rest
Encrypting data at rest is only effective if the encryption keys themselves are properly protected. HSMs provide a root of trust for key management systems, protecting master keys that encrypt and decrypt data encryption keys. This layered approach ensures that even if storage media is compromised, the data remains inaccessible without access to the HSM-protected master key. Platforms such as Fortanix Data Security Manager and Cryptomathic CKMS integrate with HSMs for enterprise key management.
Knowing which keys exist, where they are stored, and which systems depend on them is a prerequisite for effective key management. A CBOM provides this visibility, mapping cryptographic assets across your estate so that HSM-protected keys can be prioritised based on sensitivity and business impact.
IoT Device Identity Provisioning
As organisations deploy thousands or millions of connected devices, each device needs a unique cryptographic identity. HSMs generate and protect the keys used to provision device certificates at scale, ensuring each identity is created within a trusted environment. This is particularly critical in transport, energy, and defence sectors where compromised device identities could have safety-critical consequences.
How
HSM vs Software Key Storage
Organisations frequently ask whether they truly need dedicated HSM hardware or whether software-based key storage is sufficient. The answer depends on the sensitivity of the keys, regulatory requirements, and the organisation’s risk appetite. The table below provides a direct comparison.
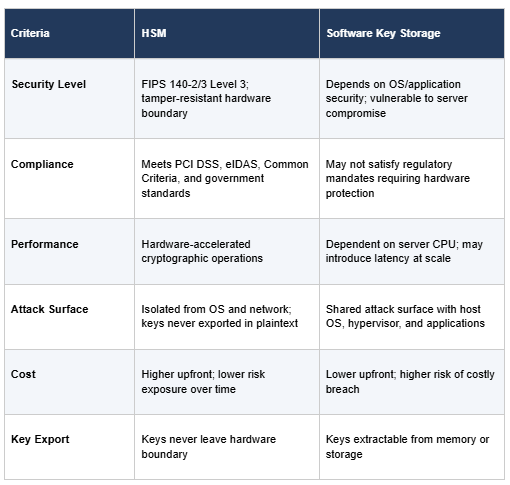
For root CA keys, payment processing keys, qualified signing keys, and any key material where compromise would have catastrophic consequences, an HSM is not optional — it is a baseline security requirement. For less sensitive use cases, software key storage with robust access controls may be acceptable, but organisations should document this risk decision formally.
Unsung’s HSM Services
Unsung is a specialist HSM and PKI consultancy delivering hardware security module services across the full lifecycle — from initial strategy and vendor selection through architecture design, deployment, migration, and ongoing operational support.
Vendor-Certified Expertise
Our consultants hold current vendor certifications across the HSM platforms we deploy. This is not theoretical knowledge — our team has hands-on implementation experience with each product in production environments across government, defence, financial services, healthcare, and critical national infrastructure.
Strategic Vendor Partnerships
Unsung maintains formal partnerships with the leading HSM vendors, giving our clients access to preferred pricing, priority technical support, and early access to new capabilities:
• Thales — Silver Partner (5+ years): Luna Network HSM 7, Luna PCIe HSM 7, Luna Cloud HSM. Our longest-standing HSM partnership, with deep expertise across the full Luna product family.
• Crypto4A — Bronze Partner: QxHSM. Quantum-safe, crypto-agile HSMs for organisations preparing for the post-quantum transition.
• Fortanix: Data Security Manager (DSM), Armor, Confidential Computing Manager. Intel SGX-based platforms delivering HSM-grade security without dedicated hardware appliances.
• Futurex: CryptoHub, VirtuCrypt, Classic Enterprise Platform. On-premises and cloud HSM solutions for payment processing, PKI, and enterprise key management.
Government and Defence Clearance
Unsung holds team members with Security Check (SC) and Developed Vetting (DV) clearance, enabling us to work on classified programmes and within secure government environments. We have delivered HSM and PKI projects for UK central government departments and defence organisations where security clearance is a prerequisite for access.
Service Types
Our HSM services encompass:
• HSM Strategy and Architecture Design: Requirements analysis, vendor evaluation, deployment model selection, and high-level/low-level design documentation.
• HSM Deployment: Physical installation, network configuration, partition creation, key ceremony facilitation, and application integration.
• HSM Migration: Moving from legacy or end-of-life HSMs to current platforms, including key migration, application reconfiguration, and validation testing.
• Operational Support: Ongoing HSM management, firmware updates, partition administration, backup and recovery procedures, and incident response.
• Training: Hands-on HSM administration training for your internal teams, covering key ceremonies, backup procedures, and day-to-day operations.
Whether you need a single HSM for a root CA offline ceremony or a multi-site, high-availability HSM estate supporting enterprise PKI, our team can help. Contact us to discuss your requirements, or explore our broader PKI Consultancy and PKI Management & Hosting services.
Frequently Asked Questions
What is a hardware security module?
A hardware security module (HSM) is a dedicated, tamper-resistant physical device that generates, stores, and manages cryptographic keys within a hardened security boundary. HSMs are validated to standards such as FIPS 140-2 Level 3 and Common Criteria, ensuring that private keys never leave the protected hardware environment. They serve as the trust anchor for PKI, code signing, payment processing, and digital signature systems.
What is FIPS 140-2 Level 3?
FIPS 140-2 Level 3 is a US government security standard for cryptographic modules administered by NIST (the National Institute of Standards and Technology). Level 3 requires physical tamper-resistance mechanisms that detect and respond to intrusion attempts, identity-based authentication for all operators, and physical or logical separation between the module’s interfaces. When tampering is detected, a Level 3 module zeroises all stored keys. The successor standard, FIPS 140-3, builds on these requirements with additional assurance levels.
Can HSMs support post-quantum cryptography?
Yes. Leading HSM vendors are actively adding support for NIST-approved post-quantum algorithms. Thales Luna 7 HSMs include firmware functionality modules for ML-DSA (formerly CRYSTALS-Dilithium), ML-KEM (formerly CRYSTALS-Kyber), and LMS/HSS hash-based signatures. Crypto4A QxHSM is designed from the ground up as a crypto-agile platform supporting both classical and post-quantum algorithms natively. For more on preparing for the PQC transition, see our guide to navigating the NIST PQC roadmap.
How much does an HSM cost?
HSM costs vary significantly depending on the deployment model, performance tier, and vendor. As a general guide:
• Network-attached HSMs: £10,000–£50,000+ per appliance, depending on partition count and cryptographic performance.
• PCIe HSMs: Generally lower per-unit cost, but require a compatible host server.
• Cloud HSMs: Monthly subscription models, typically starting from around £500/month.
Total cost of ownership should factor in professional services for deployment and integration, annual maintenance and support contracts, firmware and security updates, and staff training. Unsung provides vendor-neutral guidance on HSM selection to help you balance capability, compliance, and budget. Get in touch for a tailored assessment.
Speak to an HSM Specialist
Whether you are planning your first HSM deployment, migrating from legacy hardware, or preparing your cryptographic infrastructure for the post-quantum era, Unsung’s vendor-certified consultants can help.

