Certificate Management Protocols: CMP, ACME, EST and SCEP Compared | Unsung
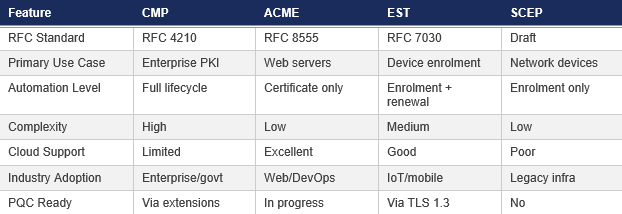
Certificate management protocols define how systems request, obtain, renew, and revoke digital certificates. Different protocols suit different use cases—what works for web server automation may not fit industrial control systems or legacy network equipment.
Understanding these protocols helps organisations select the right approach for their environment and avoid the complexity of supporting multiple protocols unnecessarily.
Certificate Management Protocol (CMP)
The Certificate Management Protocol, standardised in RFC 4210, provides comprehensive certificate lifecycle management for enterprise PKI environments. CMP distinguishes itself through self-contained security—messages include their own protection mechanisms independent of the transport layer, enabling true end-to-end security.
CMP supports complete lifecycle management: initial certificate requests, updates, renewals, and revocations all through the same protocol. It handles both client-side and server-side key generation, accommodates multiple authentication methods, and supports key pair recovery when needed.
The November 2023 updates to CMP specifications introduced a Lightweight CMP Profile tailored for industrial applications, extending the protocol's applicability to resource-constrained environments. Commercial implementations include Nexus Certificate Manager, Entrust Security Manager, and EJBCA.
Strengths
- Full certificate lifecycle support
- Strong message protection
- Mandatory proof-of-possession
- Polling, nested messages, RA/CA separation
- Transport agnostic
Weaknesses
- More complex to implement
- Requires ASN.1 handling
- Not widely supported by commercial CAs
Automated Certificate Management Environment (ACME)
ACME, defined in RFC 8555, automates certificate lifecycle operations for web-facing services. Let's Encrypt pioneered ACME, proving that fully automated certificate issuance could work at massive scale—the protocol now underlies the majority of TLS certificates issued globally.
ACME's strength lies in its automation of domain control validation through challenge-response mechanisms. The HTTP-01 challenge verifies control by placing a file on the web server. DNS-01 proves control through DNS record creation. TLS-ALPN-01 uses the TLS handshake itself for validation.
Originally designed for public web certificates, ACME is increasingly adopted for internal PKI. Many enterprise certificate management platforms now support ACME, and the Chrome Root Programme requires CA applicants to support at least one automated solution by June 2026.
Strengths
- Designed for automation at scale
- Strong security via JWS, replay prevention, and domain control validation
- Simple JSON/HTTPS interactions
- Excellent tooling (Certbot, win-acme, acme.sh)
Weaknesses
- Primarily focused on TLS server certificates
- Limited lifecycle operations compared to CMP
- Domain validation model doesn't map cleanly to device identity
Enrolment over Secure Transport (EST)
EST, defined in RFC 7030, provides a simpler alternative to CMP for certificate enrolment. It uses HTTPS as its transport, leveraging TLS for security rather than implementing protocol-level protection. This design trades CMP's flexibility for implementation simplicity.
EST suits environments where TLS infrastructure already exists and end-to-end message protection isn't required. It's commonly used for device certificate enrolment in enterprise networks, particularly for mobile device management and IoT deployments where simpler protocols reduce implementation complexity.
Strengths
- Strong security (TLS mutual auth, PoP, confidentiality/integrity via HTTPS)
- Supports enrolment, re-enrolment, CA cert retrieval, server-side keygen
- Good fit for modern devices with HTTPS stacks
Weaknesses
- More complex than SCEP (multiple endpoints, more complex structures)
- Requires full HTTPS/TLS stack, which is heavy for constrained IoT
- Less flexible than CMP
- Adoption still growing; not universal on legacy hardware
Simple Certificate Enrolment Protocol (SCEP)
SCEP emerged in the 1990s for network device certificate enrolment. Despite never achieving formal standardisation beyond an informational RFC, SCEP became widely deployed in network infrastructure—routers, switches, VPN concentrators, and similar equipment often support only SCEP.
SCEP uses HTTP transport with CMS (Cryptographic Message Syntax) for message protection. Its design reflects network device constraints: limited cryptographic capabilities, simple authentication requirements, and the need to work across vendor equipment.
While SCEP remains necessary for legacy equipment, its age shows in security limitations. Newer deployments typically favour EST or CMP where possible, reserving SCEP for devices that support nothing else.
Strengths
- Very simple to implement
- Supported by routers, switches, firewalls, MDMs, and embedded devices
- Lightweight and stable
- Good for environments where device capabilities are limited
Weaknesses
- Weaker security model
- Limited functionality: basic enrolment and renewal only
- Outdated cryptography in many implementations
- Not standards-track—RFC 8894 is Informational, not a standard
- Being replaced by EST in modern ecosystems
Choosing the Right Protocol
Selecting the right certificate management protocol is rarely a binary choice. Most enterprise environments require at least two protocols running in parallel, each serving a different segment of the infrastructure. The decision comes down to what you are issuing certificates to, how much automation you need, and what your existing estate looks like.
Use ACME when you are managing TLS certificates for web servers, load balancers, reverse proxies, or any internet-facing service where domain control validation is appropriate. ACME is the clear choice for DevOps and cloud-native environments where certificates need to be issued, renewed, and replaced without human intervention. With Chrome's Root Programme requiring automated issuance support by June 2026, ACME adoption is accelerating across both public and internal PKI.
Use CMP when you need full certificate lifecycle control across a diverse enterprise estate. CMP handles initial enrolment, renewal, revocation, key recovery, and certificate updates within a single protocol. It is the strongest option for organisations running complex PKI hierarchies with multiple certificate profiles, particularly in government, defence, and regulated industries where transport-layer independence and end-to-end message protection are requirements rather than preferences.
Use EST when you are enrolling modern devices that support HTTPS but do not need the full lifecycle capabilities of CMP. EST works well for mobile device management, IoT deployments, and environments where mutual TLS authentication is already established. It offers a practical middle ground between SCEP's simplicity and CMP's comprehensive feature set.
Use SCEP when you are supporting legacy network infrastructure — routers, switches, firewalls, and VPN concentrators that were built with SCEP support and have no EST or CMP client available. SCEP remains essential in many estates, but it should be treated as a transitional protocol. Where possible, plan a migration path toward EST for devices that support it.
AD CS\u2019s lack of native support for ACME, EST, and CMP is one of its most significant limitations for modern environments, effectively restricting organisations to SCEP and manual web enrollment. Our guide to ADCS in modern IT explores how this protocol gap affects organisations and what the replacement options are.
Implementation Considerations
In practice, effective certificate management means deploying a platform that supports all four protocols from a single management interface. Keyfactor Command is one example of a platform that natively supports CMP, ACME, EST, and SCEP alongside integrations with Microsoft ADCS, EJBCA, and public certificate authorities. This multi-protocol capability eliminates the need for separate enrolment systems per protocol and provides a unified view of your certificate estate regardless of how each certificate was issued.
When planning a deployment, consider your CA architecture first. Some protocols require specific CA configurations — CMP's proof-of-possession mechanisms and EST's mutual TLS authentication both impose requirements on the issuing CA that need to be designed in from the start rather than retrofitted. Unsung's PKI Consultancy service covers protocol selection as part of broader architecture design, ensuring the protocols you choose align with your CA platform, security policy, and operational workflows.
Performance Under Enterprise Load
Protocol performance varies significantly at scale. ACME's lightweight JSON-over-HTTPS design makes it exceptionally efficient for high-volume issuance — environments processing thousands of certificate renewals per day will see minimal overhead. CMP, by contrast, carries more message-level processing due to its ASN.1 encoding and self-contained security, which can increase latency per transaction. However, CMP's richer feature set often reduces the total number of protocol interactions needed to complete complex operations such as key recovery or certificate updates.
EST sits between the two in terms of overhead, with TLS session establishment being the primary performance factor. SCEP is lightweight by design but lacks the throughput optimisations of modern protocols.
For most enterprise deployments, protocol performance is not the bottleneck — HSM signing speed, CA database performance, and network latency between clients and the registration authority have a far greater impact on end-to-end issuance times. Organisations processing more than 10,000 certificates per day should factor load testing into their PKI Design & Build project to identify genuine constraints before they affect production.
Frequently Asked Questions About Certificate Management Protocols
What is a certificate management protocol?
What is the difference between CMP and ACME?
Is SCEP still relevant?
When should I use EST instead of SCEP?
Can I use multiple certificate management protocols at the same time?
What does Chrome's Root Programme mean for certificate management protocols?
How do certificate management protocols relate to post-quantum cryptography?
How Unsung Helps with Protocol Implementation
Unsung brings deep expertise across certificate management protocols. We help organisations evaluate their requirements and select appropriate protocols for different use cases within their environment.
Our implementation services deploy and configure protocol support across certificate management platforms including Keyfactor, Microsoft ADCS, EJBCA, and others. We integrate certificate protocols with existing infrastructure—ensuring automation works reliably across diverse systems.
Contact Unsung to discuss which certificate management protocols fit your organisation's needs.


